Complete Cyber Confidence
Stop cyber attacks dead in their tracks with CyberSmart: an all-in-one cybersecurity monitoring, optimisation, training and insurance platform proven to defend against the unexpected.
Get peace of mind with continuous compliance and round-the-clock protection.
5,000+ businesses around the UK trust CyberSmart to deliver
Complete Cyber Confidence
What is CyberSmart?
CyberSmart is the UK’s leading cybersecurity platform for SMEs who mean business when it comes to cyber defence. CyberSmart’s complete security solution for SMEs enables you to grow your business whilst protecting your most valuable assets from harm.
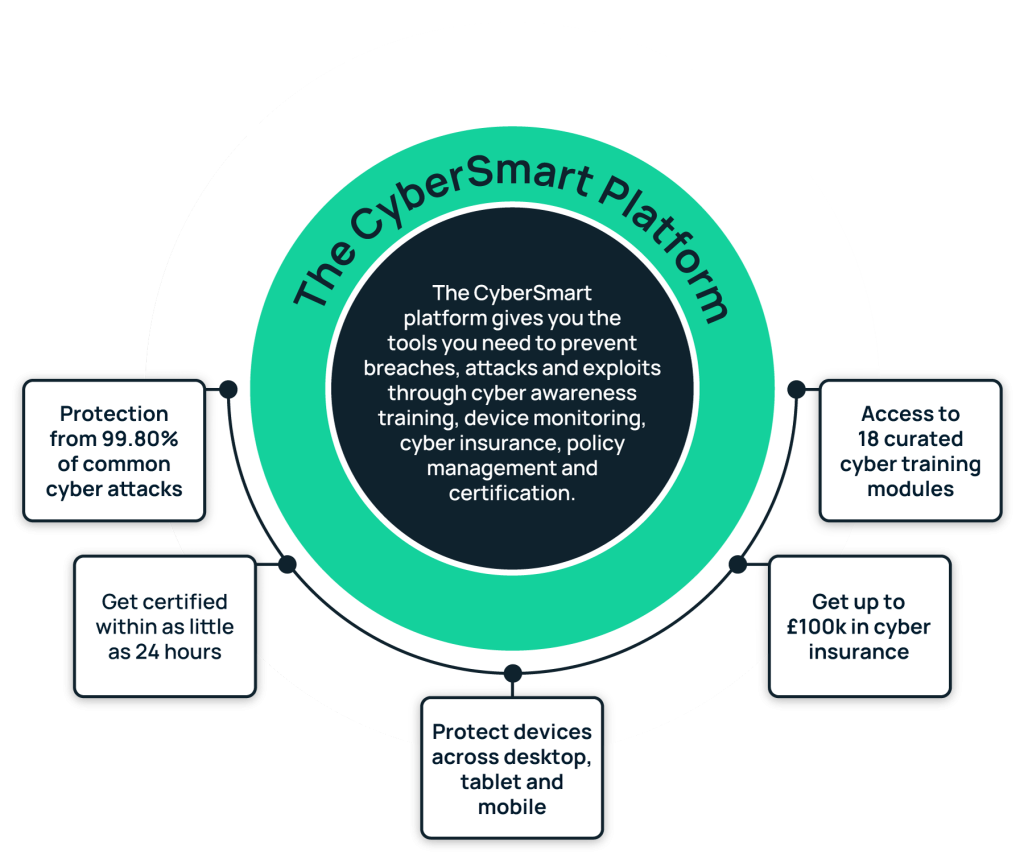
How it works
Builds the human firewall
Equip your people with the knowledge to combat cyber attacks. Enforce good cybersecurity practices and meet regulatory obligations with policy management templates and workflows. Create a strong cyber baseline and resolve gaps through government-endorsed cybersecurity certifications.
Everyday cybersecurity
Get visibility into your cyber setup and discover strengths and weaknesses across endpoints, users and overall security. Ensure your systems and devices are regularly scanned for vulnerabilities and misconfigurations through always-on monitoring. Make improvements with in-platform guidance on how to fix issues.
Financial security and recovery
Protect your business from the unexpected, with up to £100k insurance coverage and our best practice frameworks for preventing ransomware attacks. Simplify compliance with GDPR and other regulations, through Subject Access Request management, privacy policy builder and a suite of dedicated policies to maintain strong data and privacy processes.
Unparalleled scale and control
Get visibility into your cyber setup and discover strengths and weaknesses across endpoints, users and overall security. Ensure your systems and devices are regularly scanned for vulnerabilities and misconfigurations with always-on monitoring. Make improvements through in-platform guidance on how to fix issues.
Support that meets your business needs
All of this is underpinned by our world-class, UK-based support team and extensive partner network, handpicked to find you the perfect cyber solutions to fit your business needs.
Cybersecurity products
Protect yourself from 99.80% of common cyber threats





Cyber Essentials
Get protection from 99.8% of common attacks, plus
unlimited support and attempts at completing your certification.
Cyber Essentials Plus
Enjoy the added assurance of external validation for
your security by an accredited auditor.
Active Protect
Get 24/7 protection with extensive vulnerability and
device configuration scanning, policy management,
risk assessment reports and cyber security awareness training.
Ransomware & Recovery Toolbox
Defend your business against the unexpected through
risk and business continuity plans, combined with our
free £100k cyber insurance.
Privacy Toolbox
Meet your business’ regulatory requirements with
dedicated workflows, support, assessments
and privacy policies. Give your customers peace of
mind, by proving your GDPR credentials and
providing customers with a process to ask questions
about their data.
Interactive Demo
What our customers says
Hot off the press, our latest cybersecurity reports and insights
Awards
Security Vendor of the Year – SME
Computing Security Excellence Awards

Cyber Security Vendor of the Year
Technology Reseller Awards

Tech Growth Business of the Year
National Technology Award

CyberTech 100
2023
Global List

Partner with the UK’s leading cybersecurity solution for SMEs
Provide scalable cybersecurity monitoring, training and insurance with an all-in-one solution. Boost your service offerings, build strong client relationships and add market-leading SME cybersecurity to your product bundles. Access exclusive discounts, marketing development funds, free certification and vulnerability scanning.

Enro Ltd t/a Superscript is authorised and regulated by the Financial Conduct Authority. Individual cover purchased online is offered on a standardised, non-advised basis and is not bespoke. Terms, conditions and coverage limits are predetermined by the Underwriter. If you require bespoke coverage offered on an advised basis, please contact our in-house broking team.