According to research from popular exercise app Strava, the second Friday of January is “quitters’ day”– the day when people are most likely to give up on New Year’s resolutions.
It’s the day when all those promises made in good faith back in December go up in smoke. Running shoes across the land are hurled to the back of the nearest cupboard, never to see the light of day again. Gym memberships are forgotten about. And new hobbies fall by the wayside.
The biggest problem with most New Year’s resolutions is their difficulty. Sure, the long-term gains might be amazing, but what about the months of pain and effort to get there?
But not all resolutions have to be difficult or doomed to failure. Take, for example, our list of easy cybersecurity New Year's resolutions.
Unlike attempting a couch to 5k or taking up a new hobby, they don’t require hours of your time to see results. Nor do you need to go out and buy expensive new tools or overhaul existing processes. All it takes is a few tweaks here and there to get your business’s cybersecurity fighting fit for the year ahead.
And the best part? Once you’re in the habit, you’re unlikely to break them.
1. Start patching and updating software regularly
We bang the patching drum a lot at CyberSmart. Regular readers of our blog will have noticed we mention it at every possible opportunity. But, as repetitive as it might be, there’s a very good reason behind our love affair with patching.
Regularly updating your software and operating systems is the easiest, most time-efficient way to improve your cybersecurity. Even, the best software becomes outdated or develops gaps and, when it does, cybercriminals suddenly have an easy route into your business.
Fortunately, avoiding the worst is incredibly easy and it shouldn’t take you more than a couple of minutes each month. All it requires is that you check every now and then for any new updates to tools and software you use. Or, if you want an even easier solution, simply turn on auto-updates in your device’s settings, and you won’t even have to think about it.
To learn more about patching, check out our recent blog on the subject.
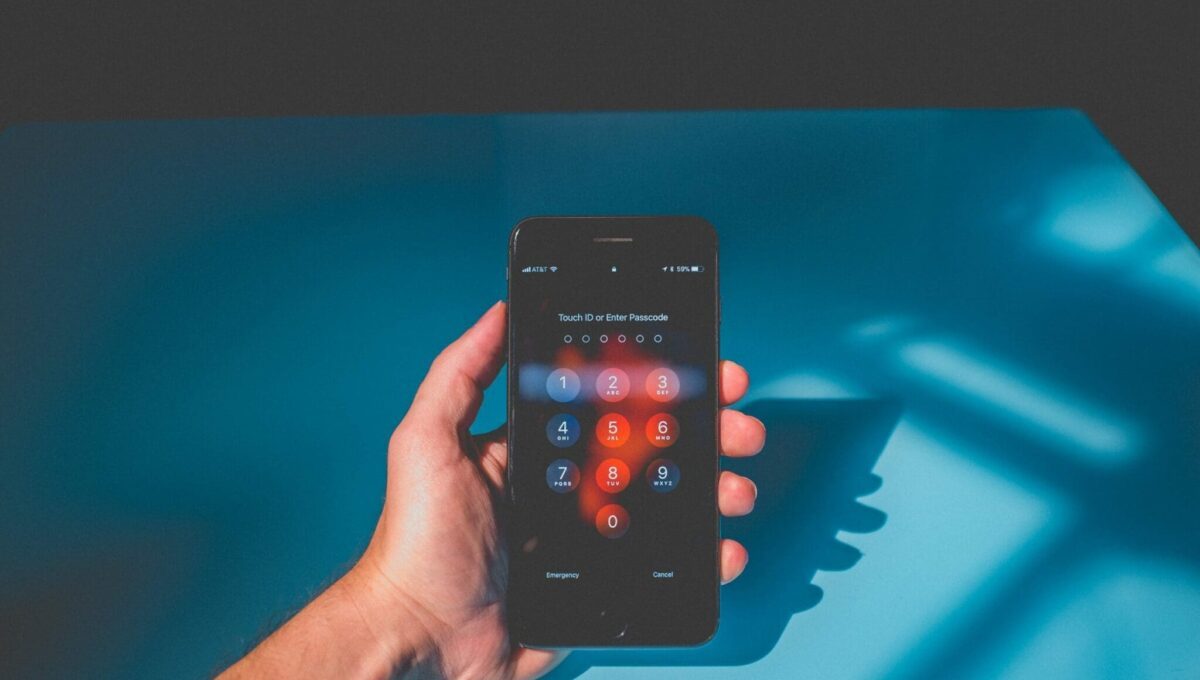
2. Create a password policy
Of all the resolutions on this list, creating a secure password policy is by far the simplest. Most of us know the importance of strong passwords, but that doesn’t stop us using the same easily-guessable phrase we’ve been using since 2001 for everything. We’re only human after all.
The problem is this poses a huge security risk. It only takes a cybercriminal to crack one insecure password in your business for disaster to strike. But the good news is fixing it is simple.
Set up a password policy and ensure everyone in the business follows it. Often, it doesn’t take much more than a well-worded email and a few friendly nudges to get everyone on board.
What should go in the policy? Well, a strong password policy should have four key points:
- Use complex passwords that are a combination of letters, numbers and symbols. In-built browser tools like Google Chrome’s password generator are great for this
- Change passwords regularly
- Set up different passwords for different accounts, tools and software. If you struggle with remembering them, consider using a secure password manager tool like LastPass or 1password
- Use two-factor authentication (2FA) wherever possible
3. Use encryption
Encryption is one of those technologies that everyone has a vague notion they should be using. However, many of us get put off by misconception that it’s difficult to set up or hard to understand if you’re not a techy type.
In reality, this couldn’t be further from the truth. You probably already use encryption a lot in your daily life, you just don’t know it. Ever sent a message using WhatsApp? That’s encryption. Bought something from a web store? Encryption.
We won’t go into exactly how it works (if you’d like to know more we have a whole blog on the subject) but, essentially, encryption randomises data so that only an authorised recipient with a key can see it.
Due to the complexity of the randomisation process, encryption is near impossible to break so it offers a level of security passwords alone can’t match. Better still, once you’ve set it up and are used to using it, it’s unlikely you’ll ever have to think about it again.
4. Make cybersecurity part this year’s budget
Attacks on SMEs now account for 58% of all cybercrime. What’s more, small businesses’ ability to absorb an attack is limited. Research from insurance and risk consultancy firm, Gallagher, found that over 50,000 UK SMEs would collapse if hit by a cyberattack.
Given the risks, you would expect cybersecurity to be top of most businesses’ budgeting lists. However, that’s often not the case. It’s not hard to see why; if you’re an SME performing financial wizardry each year just to keep things ticking over, cybersecurity can feel like a ‘nice to have’ rather than a priority. It’s this that leads to many smaller businesses making do with anti-virus and little else.
Unfortunately, firms who do this are playing Russian roulette without being conscious of it. Sooner or later, an enterprising cybercriminal will take advantage of weak defences, no matter how small your business. It’s a simple thing, but make 2021 the year cybersecurity features in your annual budget.
5. Get Cyber Essentials certified
If you’ve heard of Cyber Essentials, you’re likely questioning this suggestion. Isn’t Cyber Essentials certification a long, drawn-out process that takes weeks to complete? It’s hardly fitting for a list of ‘easy’ resolutions.
Well, the truth is that getting Cyber Essentials certified can be like that. However, it doesn’t have to be. At CyberSmart we offer a Cyber Essentials certification process that can take as little as 24 hours, with no need for constant back and forth. We’ll tell you whether you’re going to pass before you submit and help you address any problems, so you only need to do it once.
Getting Cyber Essentials certified is a requirement for many government tenders and can protect your business from 98.5% of cybersecurity threats. But the benefits don’t end there. It’s also a great indicator of your business’s commitment to security, marking you out as trustworthy and safe to potential partners and customers.
So concludes our 2021 cybersecurity New Year’s resolutions. Although we’d recommend doing everything we’ve suggested, even adopting just one will noticeably improve your business’s cybersecurity. So why not kick the year off with a resolution you’ll keep?
Looking to improve your cybersecurity but not sure where to begin? Start 2021 the right way, by getting certified in Cyber Essentials, the UK government scheme that covers all the fundamentals of cyber hygiene.