Are you considering Cyber Essentials Plus, but unsure whether it’s right for your business? To help you decide, we’ve pulled together a quick summary of how the government-backed certification works, and why it could be the next step for your business. Read on to find out more.
What is Cyber Essentials Plus?
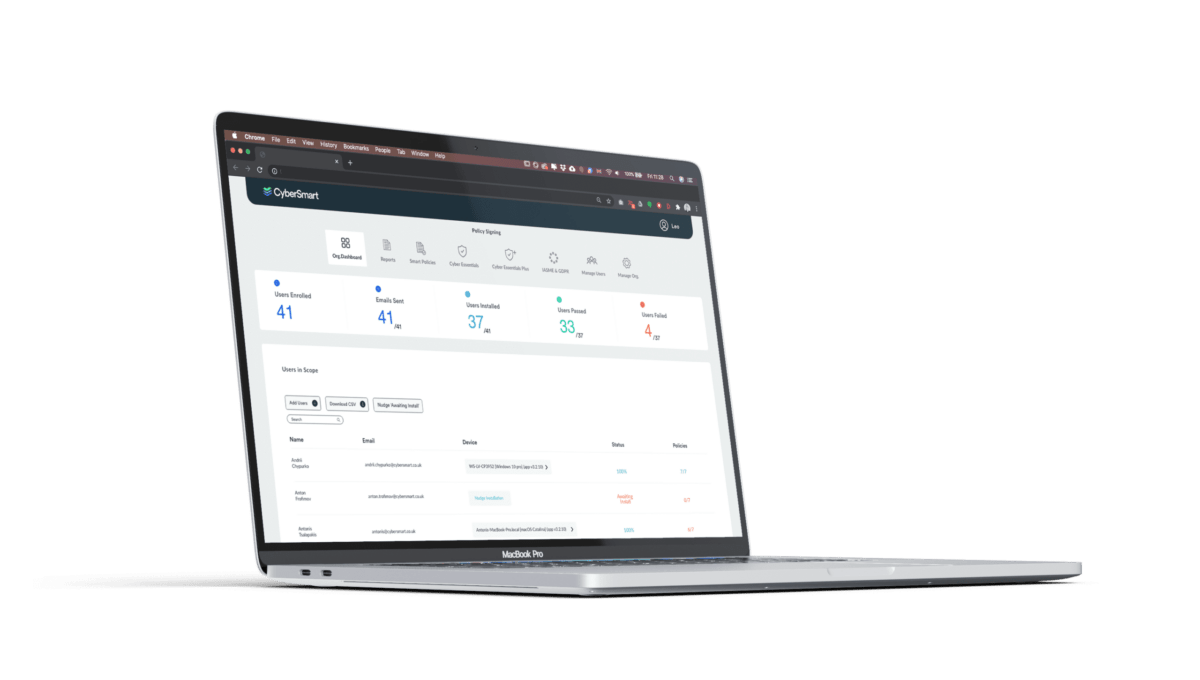
Cyber Essentials Plus follows the same simple approach and offers the same benefits as Cyber Essentials. However, it differs in one key aspect; Cyber Essentials Plus includes a technical audit of your system. The controls are the same, the audit just ensures they’re in place and properly configured.
The audit process takes a little more effort than the standard certification, but it’s worth it for the peace of mind that your security is up to standard.
When should you consider Cyber Essentials Plus?
The truth is, any business looking to improve its security could benefit from Cyber Essentials Plus. However, there are a few scenarios in which we’d recommend Cyber Essentials Plus.
Confused about certification? Read our free guide for everything you need to know.
1. You want a thorough assessment of your cybersecurity credentials
Cyber Essentials is a great first step for any small business that wants to up its cybersecurity game. Nevertheless, the standard Cyber Essentials certification is self-assessed. This means that while you’ll have to comply with the security controls it lays out to pass, you won’t benefit from an independent assessment.
Cyber Essentials Plus, on the other hand, features a visit (either in person or remotely) from an independent auditor. So you’ll gain the peace of mind that your security credentials are up to scratch.
2. You want to work with high-value customers
It’s a general rule of thumb that the more prestigious the clients you work with, the more stringent their security requirements. Cyber Essentials Plus can help demonstrate to potential customers with high expectations that you take data protection and cybersecurity seriously. And, it could help you steal a march on competitors.
3. You’re a public-facing business
Any business that directly interacts with the public should make cybersecurity a top priority. If your business stores personal data, whether that’s contact details or financial information, it’s part of your duty of care to protect it.
Investing in Cyber Essentials Plus will not only help you put in place the measures needed to better protect your organisation, but it also demonstrates to customers that you take security – and their personal data – seriously.
4. You work in a sector that requires higher-than-standard security
Some industries are more at risk from cyberattacks than others. For example, manufacturing firms were the victims in almost a quarter (24.9%) of all breaches globally in 2022, closely followed by finance and insurance with nearly a fifth (18.9%).
If your business works in a high-risk sector, it’s natural that you need better protection. Again, the standard certification is a great stepping stone, but the extra assessment and validation provided by Cyber Essentials Plus is key if you’re more likely to be targeted.
What’s more, many businesses working in high-risk industries will require partners and suppliers to demonstrate better-than-basic credentials and Cyber Essentials Plus fulfils this function.
5. You want to access government funding or bid for tenders
Although Cyber Essentials Plus isn’t mandatory for all government funding and contracts yet, there are plenty of scenarios where you’ll need it. For instance, schools and colleges hoping to secure ESFA Education and Skills contracts are required to have passed Cyber Essentials and be working towards Cyber Essentials Plus.
Likewise, many healthcare and defence tenders mandate that applicants have, at least, the standard certification in place, if not Cyber Essentials Plus. There’s even a case to be made for investing in Cyber Essentials Plus even if the contract doesn’t require it. In a competitive tendering process, being able to demonstrate you have better security bona fides than your rivals could help tip the balance in your favour.
Still unsure about which cybersecurity certification is right for your business? Check out our guide to UK certifications for everything you need to know.