Managing and monitoring cybersecurity across an entire supply chain is a challenging task. This is especially true if you're an SME. However, knowledge and prevention strategies can greatly reduce the risk of a successful supply-chain attack. And, this can be extended to the suppliers and third parties in your supply chain.
Ultimately, the best way to improve your cybersecurity is to create a cohesive, collaborative environment that helps drive continuous security improvement internally and across your supply chain. We’ll explore how to do exactly that in this blog.
Why worry about supply chain attacks?
Supply chain attacks are nothing new but, now more than ever, businesses are accelerating their efforts to prevent them. The National Cyber Security Centre (NCSC) issued new guidance following the recent rise in supply chain attacks, revealing that only one in ten businesses review the risks posed by their immediate suppliers. Similarly, 44% of organisations say they will substantially increase their year-over-year spending on supply chain cybersecurity in the coming year.
So there's never been a better time to work with your suppliers to identify risks and ensure appropriate security measures are in place. To help you out, here are five simple steps.
5 steps to encourage continuous security improvement for supply chains
1. Understand the basics of cybersecurity
Begin by looking at your organisation. In today’s digital world, the bare minimum of cybersecurity isn’t enough. SMEs are often limited by knowledge and budget, but luckily, there are many accessible solutions to help improve your cybersecurity credentials. Government-backed schemes like Cyber Essentials require you to meet specific cybersecurity standards. By achieving accreditation, you’ll ensure you’re covering the basics. And, with this knowledge, you’re better prepared to assess your supply chain.
Want to know more about the risks posed by supply chains? Read our guide.
2. Conduct a risk assessment
Your supply chain might be extensive with many moving parts and people. Equally, it could be very small. No matter the size, take the time to conduct a thorough cybersecurity risk assessment of your supply chain. This might be asking suppliers whether they have cybersecurity accreditations, such as a Cyber Essentials certification, that help them stay secure and compliant.
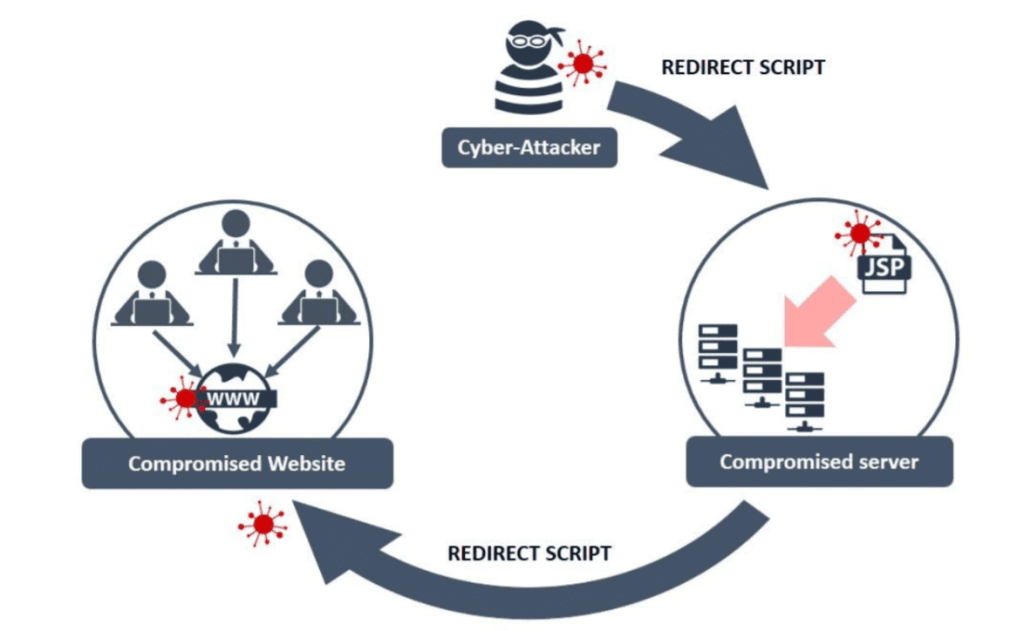
Look for specific risk factors in your supply chain. For example, payment processing software might be more susceptible to skimming attacks. Does your provider have cybersecurity measures to mitigate against this? It’s happened to even established and seemingly secure businesses, so it could happen to your providers.
3. Define contractual agreements
If you want to ensure everyone you work with takes cybersecurity seriously, the simplest step is to write cybersecurity requirements into your contracts with third parties and suppliers. This will allow you to define your expectations for
cybersecurity and procedures for communicating and reporting incidents – making everybody safer in the process.
4. Encourage cybersecurity training
Certifications and contractual agreements can’t totally override human error. You already know your employees should receive cybersecurity training, but do your supply chain contacts also offer it to their employees? Consider making your partners aware of platforms to enhance employees’ cybersecurity training. While this is ultimately your suppliers’ responsibility, open communication about what’s available is beneficial and shows you prioritise cybersecurity.
5. Collaborate and share intelligence
Staying up to date with the latest cybersecurity news is a great method of staying aware of potential risks. Not all SMEs will have dedicated cybersecurity professionals to hand, so following news sources or trusted cybersecurity blogs can help you keep your knowledge up to date.
It’s wise to share your findings with partners in your supply chain. This might be through a monthly email chain, communication channel like Microsoft Teams, or within your regular meetings. Open communication is key to improving collaboration with your supply chain and demonstrates a desire for a unified effort towards increased cybersecurity.
Conclusion
The importance of supply chain cybersecurity can’t be understated in today’s landscape. Ian McCormack, Deputy Director for Government Cyber Resilience at the National Cyber Security Centre emphasises this in a recent statement;
“Supply chain attacks are a major cyber threat facing organisations and incidents can have a profound, long-lasting impact on businesses and customers. With incidents on the rise, it is vital organisations work with their suppliers to identify supply chain risks and ensure appropriate security measures are in place.”
Luckily, the road to improved and continuous supply chain security isn’t complex. By taking simple measures, such as a cybersecurity certification and collaborating closely with suppliers, your business will become more secure.